We are sitting at the intersection of cybersecurity and artificial intelligence in the enterprise, and there is much to know and do. Our goal is not just to keep you updated with the latest AI, cybersecurity, and other crucial tech trends and breakthroughs that may matter to you, but also to feed your curiosity.
Thanks for being part of our fantastic community!
Welcome to the first edition of our new format aimed at providing you more value:
Did You Know - The Education Sector Breach
Strategic Brief - The Canvas Hack and the New Pay-or-Leak Economics
Threat Radar
The Toolkit
AI & Cybersecurity News & Bytes
C-Suite Signal
Byte-Sized fact
Get my latest book on Cyber Insurance. Available on Amazon, Barnes&Noble, Apple Books, and more…

Cyber insurance has become one of the biggest challenges facing business leaders today with soaring premiums, tougher requirements, denied claims, AI-powered attacks, and new SEC disclosure rules that punish slow response.
If you're responsible for cyber insurance risk management, cyber liability insurance decisions, or answering to the board, you need a playbook — not guesswork.
A Leader's Playbook To Cyber Insurance gives you a clear, practical roadmap for navigating today's chaotic cyber insurance market.
💡 Did You Know - SaaS Supply Chain Risk
Did you know that ShinyHunters claims to have stolen personal data from 275 million users on Instructure's Canvas learning platform?
Did you know that Instructure first detected the unauthorized activity on April 29 and notified affected schools on May 5, giving districts a one-week sprint to assess exposure?
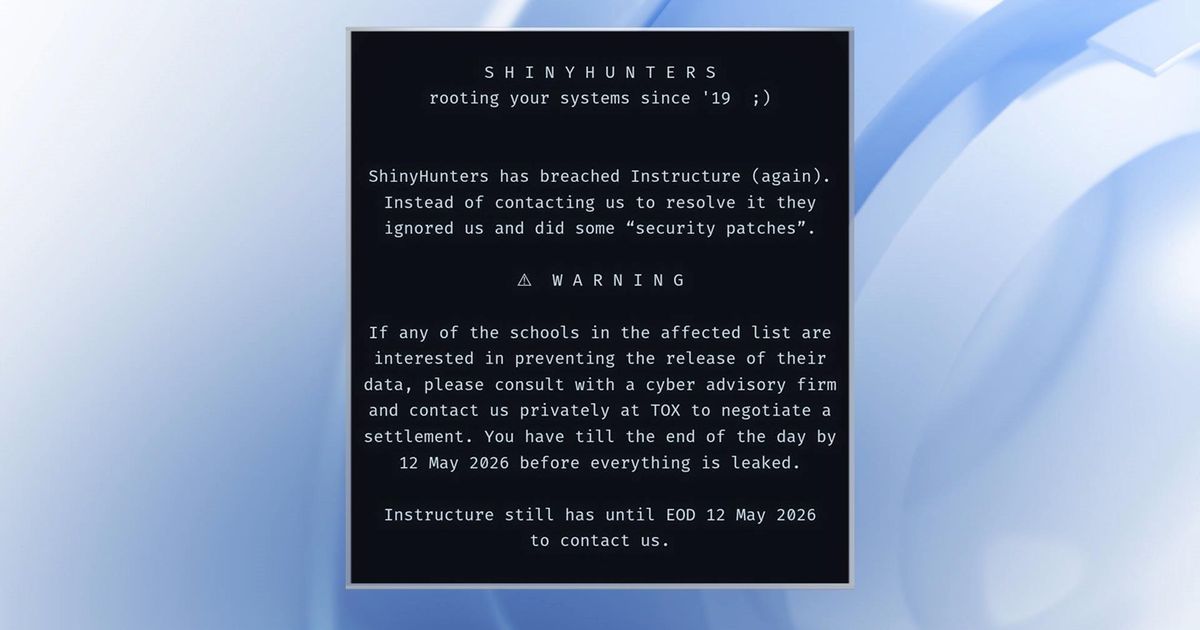
Did you know that the threat actor gave schools until May 12 to negotiate a settlement, after which the data goes public on the leak site?
Did you know that Cushman & Wakefield, hit by the same ShinyHunters group this week, lost more than 500,000 Salesforce records including PII and internal corporate data?
Did you know that Trellix — yes, the security vendor — disclosed attackers gained access to the source code of its security products, meaning the same code defending your endpoints is now being studied for weaknesses?
Did you know that 87% of ransomware claims in 2025 entered through remote access services, up from 80% the year before?

🎯 STRATEGIC BRIEF:
The Trusted Vendor Problem
Look, the education sector got hit hard this week, and the way it got hit matters more than the headline.
ShinyHunters, the same group also tied to the Cushman & Wakefield and Medtronic intrusions in the same week, claims to have lifted personal data on 275 million users from Instructure's Canvas, the dominant learning management system in U.S. K-12 and higher ed. Names. Email addresses. Internal IDs. Possibly more, depending on which district. Instructure detected the activity on April 29, revoked access, hired forensics, and notified schools on May 5. Then the extortion clock started.
The Issue
The shape of this attack is what should scare every C-suite, not just superintendents. The threat group is not asking Instructure for a ransom. They're going downstream — to every school district that uses Canvas — and demanding individual settlements before the May 12 leak deadline. That's a one-vendor compromise turned into a thousand-customer extortion campaign.
We've seen this play before in healthcare and accounting. Now it's hitting education, where IT staff are thin, legal counsel is shared across districts, and parents are politically loud. Districts that have never seen a six-figure ransom demand in their lives are now staring one down with a hard deadline and minimal forensic visibility into what was actually taken from their slice of the Canvas tenant.
Cushman & Wakefield got the same treatment with 500,000 Salesforce records exposed. The pattern is identical. Compromise the SaaS vendor, scrape what you can, then run an extortion auction with each downstream customer as a separate target.
The Opportunity
Here is the part nobody talks about. This shift exposes a real gap in how most organizations buy SaaS. Almost every Canvas contract — and almost every Salesforce, Workday, ServiceNow, and Microsoft 365 contract — pushes data classification, breach notification, and incident response responsibility back to the customer. Not the vendor. You.
What's emerging in response is a pragmatic SaaS security posture management (SSPM) market — companies like AppOmni, Adaptive Shield (now Crowdstrike Falcon Shield), and Obsidian Security — that finally gives security teams visibility into who has access to what inside a SaaS tenant, what data is exposed externally, and what configurations are dangerous. According to recent vendor data, organizations using SSPM tooling reduce mean time to detect SaaS misconfigurations by roughly 70%.
The other shift is on the insurance side. Cyber insurers are waking up to "downstream extortion" as a separate claim type. Resilience and Coalition both flagged this in their April loss reports. Expect to see ransomware exclusions tighten, sub-limits appear for SaaS-vendor breaches, and more questionnaires asking about SSPM coverage in 2026 renewals.
Why It Matters
For boards, this story is not "another breach." It's a structural change in vendor risk. You bought a learning platform, a real estate platform, a CRM. You did not buy the legal risk of being one of 100,000 districts on a ransom group's spreadsheet. But that's where you are.
Liability in these cases is messy. Schools are subject to FERPA. Companies are subject to state breach laws plus, increasingly, FTC oversight on data handling. Boards that say "the vendor is responsible" are going to find that argument doesn't survive a deposition.
The Playbook
Demand the Tenant Map: Inside 14 days, get every SaaS owner in your org to list which platforms they use, who the admin is, and what data sits inside. If your name is on the company's cyber insurance application, you need this map before renewal.
Build a SaaS Breach Runbook: Treat a SaaS-vendor breach like a tabletop exercise this quarter. Your existing IR plan probably assumes the breach is on infrastructure you control. The Canvas pattern says it won't be.
Force Vendor Accountability into Renewals: Add specific contractual language for breach notification timelines (under 72 hours), forensic cooperation, and customer-level forensic data delivery. Vendors will push back. That's the point — if they won't commit, route the budget to one who will.
Cybersecurity is no longer just about prevention—it’s about rapid recovery and resilience!
Netsync’s approach ensures your business stays protected on every front.
We help you take control of identity and access, fortify every device and network, and build recovery systems that support the business by minimizing downtime and data loss. With our layered strategy, you’re not just securing against attacks—you’re ensuring business continuity with confidence.
Learn more about Netsync at www.netsync.com
📡 THREAT RADAR - Rapid intelligence on active threats
Instructure Canvas (Education LMS):
Risk: High — credential and data exfiltration via SaaS supply chain compromise.
Impact: ShinyHunters claim 275M user records including PII; districts face individualized extortion through May 12 deadline.
Action: Immediately rotate any admin credentials and API tokens tied to Canvas, audit OAuth grants, and deploy SSPM coverage if you haven't already.
Palo Alto Networks PAN-OS (CVE under active exploit):
Risk: Critical — buffer overflow in the User-ID Authentication Portal, CVSS 9.3 / 8.7.
Impact: Threat actors attempted exploitation as early as April 9; successful exploitation gives attackers initial access into the perimeter.
Action: Apply the Palo Alto patch immediately on any exposed PAN-OS appliance and check authentication portal logs back to early April.
Trellix Source Code Theft:
Risk: High — vendor source code exposure.
Impact: Attackers can study Trellix product internals to find unpatched weaknesses they can use against deployed customers.
Action: Verify Trellix product version baselines, monitor vendor advisories closely, and segment endpoints behind compensating controls until Trellix issues guidance.
🛠️ THE TOOLKIT - Solutions for the Post-MFA Era
Solutions for SaaS supply chain security
The SaaS Visibility Layer: AppOmni
Problem: Your security team has no idea what's actually configured inside your Canvas, Salesforce, or Workday tenants.
Solution: Continuous posture management for 100+ SaaS apps, with automated detection of dangerous misconfigurations and external data exposure.
The Identity Recovery Tool: Push Security
Problem: You can't tell which users had their SaaS credentials harvested in the latest breach.
Solution: Browser-based identity threat detection that catches credential theft, session hijacking, and shadow SaaS in real time.
The Vendor Risk Engine: SecurityScorecard
Problem: You have hundreds of SaaS vendors and zero ongoing visibility into their security posture.
Solution: External rating and continuous monitoring of vendor security hygiene, with alerts when a vendor's risk profile changes.
Artificial Intelligence News & Bytes 🧠
Cybersecurity News & Bytes 🛡️
Speak naturally. Send without fixing.
Wispr Flow turns your voice into clean, professional text you can send the moment you stop talking. Not rough transcription you have to clean up. Actual polished text — ready for email, Slack, or any app.
Speak the way you think. Go on tangents. Change your mind mid-sentence. Flow strips the filler, fixes the grammar, and gives you text that reads like you spent five minutes writing it.
89% of messages sent with zero edits. Millions of professionals use Flow daily, including teams at OpenAI, Vercel, and Clay. Works on Mac, Windows, and iPhone.
📊 C-SUITE SIGNAL - Key talking points for leadership
Key talking points for leadership
SaaS is now the supply chain. The Canvas, Cushman, and Medtronic incidents this week share one shape: compromise a vendor, then run a thousand individual extortion plays. If your board still treats SaaS as "outsourced and out of mind," update the slide.
Cyber insurance won't save you from downstream extortion. Resilience and Coalition both flagged this risk class in April. Expect tighter sub-limits and exclusions for SaaS-vendor breaches at your next renewal. Read the policy this quarter, not the morning of an incident.
🧠 BYTE-SIZED FACT
In 1988, a single floppy disk labeled "AIDS Information" was mailed to 20,000 attendees of a WHO conference. It was the first ransomware attack on record. The ransom: $189, payable to a P.O. box in Panama.
The Lesson: The economics of extortion haven't changed in 38 years. Only the scale and the delivery mechanism. The Canvas attack is the AIDS Trojan with a JSON file and 275 million victims.
Found this valuable? Forward this to your team. The Cybervizer Newsletter
Questions, Suggestions & Sponsorships? Please email: [email protected]
Also, please subscribe (It is free) to my AI Bursts newsletter that provides “Actionable AI Insights in Under 3 Minutes from Global AI Thought Leader”.
You can follow me on X (Formerly Twitter) @mclynd for more cybersecurity and AI.

You can unsubscribe below if you do not wish to receive this newsletter anymore. Sorry to see you go, we will miss you!