We are sitting at the intersection of cybersecurity and artificial intelligence in the enterprise, and there is much to know and do. Our goal is not just to keep you updated with the latest AI, cybersecurity, and other crucial tech trends and breakthroughs that may matter to you, but also to feed your curiosity.
Thanks for being part of our fantastic community!
Welcome to the first edition of our new format aimed at providing you more value:
Did You Know - The Defender Shortage
Strategic Brief - Three Attacks, One Story
Threat Radar
The Toolkit
AI & Cybersecurity News & Bytes
C-Suite Signal
Byte-Sized fact
Get my latest book on Cyber Insurance. Available on Amazon, Barnes&Noble, Apple Books, and more…

Cyber insurance has become one of the biggest challenges facing business leaders today with soaring premiums, tougher requirements, denied claims, AI-powered attacks, and new SEC disclosure rules that punish slow response.
If you're responsible for cyber insurance risk management, cyber liability insurance decisions, or answering to the board, you need a playbook — not guesswork.
A Leader's Playbook To Cyber Insurance gives you a clear, practical roadmap for navigating today's chaotic cyber insurance market.
💡 Did You Know - Medical Device Cybersecurity
Did you know that there are roughly 35,000 chief information security officers covering an estimated 359 million organizations worldwide? That is a 10,000-to-1 ratio.
Did you know that just 22% of state government CISOs say their data is protected from cyberthreats, the lowest confidence level in the history of the NASCIO-Deloitte study?
Did you know that the SharePoint zero-day disclosed last week (CVE-2026-32201) is being actively exploited and allows full remote code execution against unpatched servers?
Did you know that the malicious versions of the Python "Lightning" package (2.6.2 and 2.6.3, published April 30) sat in the public registry for hours before takedown, long enough to seed thousands of CI/CD pipelines?
Did you know that the Medtronic incident this week, attributed to ShinyHunters, exposed millions of patient records and is the third major medical device firm hit in the last 90 days?
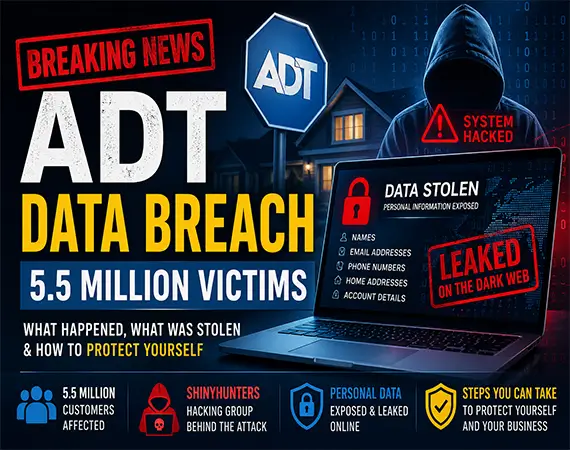
Did you know that the ADT breach disclosed this week affected over 5.5 million customers, including home address and alarm code data?

🎯 STRATEGIC BRIEF:
When Devices Become Weapons
I want to walk you through the week we just had, because the headlines made it sound like three separate stories. They weren't. They were one story told three times.
Story one. Microsoft's SharePoint platform got hit with a critical zero-day, CVE-2026-32201. Remote code execution. Already being exploited in the wild. If you run on-prem SharePoint, an attacker with a network path can take the box.
Story two. The Python "Lightning" package, used by tens of thousands of developers in the AI and ML world, had two malicious versions pushed to the public registry on April 30. They were live long enough to land in CI pipelines, harvest credentials, and call home before anyone noticed.
Story three. The new NASCIO-Deloitte report dropped, and the headline number was brutal. Just 22% of state CISOs feel confident their data is defended. The rest are openly saying their budgets are the worst they have seen in a decade.
The Issue.
Three different attacks. Three different surfaces. One uncomfortable thread connecting them. Every defender you have is now responsible for an attack surface that grew faster than the team did.
The SharePoint zero-day works because patching cycles in most enterprises still run two to four weeks. The Lightning package works because nobody pinned dependencies tightly enough to catch a same-day malicious version. The state CISO crisis works because we have spent ten years adding cloud, SaaS, AI, and IoT to the perimeter while keeping headcount roughly flat.
35,000 CISOs. 359 million organizations. The math does not work.
The Opportunity. This is where AI actually earns its keep on the defender side. Not chatbots for SOC analysts. Not vendor demos at RSA. The real opportunity is autonomous patch validation, autonomous dependency scanning, and autonomous tier-one triage so your scarce human defenders are spending time on the 5% of decisions that actually require judgment.
Anthropic released Mythos this month with explicit positioning around cybersecurity applications. Microsoft Security Copilot is now closing 60% of low-severity incidents without human touch. Google's Big Sleep agent is finding zero-days in open source faster than any human team. The technology is here. The question is whether you are deploying it as a force multiplier or watching demos and waiting.
Why It Matters. Your business does not have a CISO problem. Your business has a coverage problem. Coverage is a function of attack surface divided by skilled defenders. Attack surface is doubling every 18 months. Defender supply is flat to declining.
You either change the denominator (cut surface area, kill unused SaaS, reduce on-prem exposure) or you change the numerator (force multiply your existing team with AI-driven defense). Most companies are doing neither. They are buying more dashboards.
The Playbook:
Patch Inside 48 Hours: Set an absolute SLA for critical CVEs that does not bend for change windows. CVE-2026-32201 is still unpatched in many enterprises eight days after disclosure. That is not a process problem. That is a willingness problem.
Pin Every Dependency: Mandate exact-version pinning in all production manifests, with weekly automated audits against the registry for replaced or yanked versions. The Lightning attack would have failed in any environment that pinned to 2.6.1.
Buy Your CISO an AI Team: Allocate a real budget line (not a pilot, a budget line) for autonomous defense agents this fiscal year. Pick one of: Microsoft Security Copilot, Crowdstrike Charlotte AI, or Sentinel One. Deploy in production, not in a sandbox.
Cybersecurity is no longer just about prevention—it’s about rapid recovery and resilience!
Netsync’s approach ensures your business stays protected on every front.
We help you take control of identity and access, fortify every device and network, and build recovery systems that support the business by minimizing downtime and data loss. With our layered strategy, you’re not just securing against attacks—you’re ensuring business continuity with confidence.
Learn more about Netsync at www.netsync.com
📡 THREAT RADAR - Rapid intelligence on active threats
Microsoft SharePoint Server (CVE-2026-32201):
Risk: Critical, Remote Code Execution
Impact: An unauthenticated attacker with network access to a SharePoint server can execute arbitrary code at SYSTEM level, taking full control of the host and any connected document libraries.
Action: Apply Microsoft's emergency out-of-band patch immediately. If patching is not possible, isolate SharePoint servers behind a WAF or restrict to VPN-only access today.
Python Lightning package (versions 2.6.2 and 2.6.3):
Risk: High, Supply Chain Credential Theft
Impact: Both versions ship malicious code that exfiltrates environment variables, AWS credentials, and SSH keys to an attacker-controlled endpoint. Anywhere these versions ran, assume credentials are burned.
Action: Audit pip install logs across all CI/CD pipelines from April 30 onward. Pin to 2.6.1 or earlier. Rotate any credentials present on machines that pulled the bad versions.
Linux Local Privilege Escalation (CVE-2026-31431):
Risk: High (CVSS 7.8), Local Privilege Escalation
Impact: An attacker with low-privilege local access can escalate to root, useful as a second-stage exploit after initial compromise via web shell or compromised container.
Action: Apply distribution patches as they roll out this week. Audit container images for vulnerable kernel versions and rebuild base images.
🛠️ THE TOOLKIT - Solutions for the Post-MFA Era
The Patch Accelerator: Action1
Problem: Critical patches sit unapplied for weeks because IT has too many machines and too few people.
Solution: Cloud-native patch automation that handles third-party apps and OS updates with policy-driven rollouts, free for up to 200 endpoints.
The Dependency Watchdog: Snyk
Problem: Malicious packages enter your build before anyone notices.
Solution: Real-time scanning of every dependency change against known-bad and behaviorally-suspicious packages, with auto-blocking in CI before the build proceeds.
The Autonomous Tier 1: Microsoft Security Copilot
Problem: Your SOC drowns in low-severity alerts that still need investigation.
Solution: AI-driven triage that handles roughly 60% of tier-one incidents end to end, freeing human analysts for the alerts that actually matter.
Artificial Intelligence News & Bytes 🧠
Cybersecurity News & Bytes 🛡️
Your inbox is full. Slack is piling up. Client messages need a response yesterday. Typing thoughtful replies to all of it takes hours you don't have.
Wispr Flow turns your voice into clean, professional text you can send the moment you stop talking. Speak like you would to a colleague — tangents and all — and get polished output. Emails, Slack, LinkedIn, WhatsApp, whatever's open.
89% of messages sent with zero edits. Used by teams at OpenAI, Vercel, and Clay. Works on Mac, Windows, and iPhone.
📊 C-SUITE SIGNAL - Key talking points for leadership
The Coverage Equation Is Broken: Your attack surface has doubled in 18 months while your security headcount has not. Stop benchmarking against industry peers, who are equally exposed, and start benchmarking against your own surface area.
Cyber Insurance Is Repricing in Real Time: Carriers are watching the SharePoint and supply chain attacks closely and are quietly tightening exclusions on unpatched-CVE losses and unpinned-dependency losses. Your renewal in Q3 may not look like your policy in Q1.
🧠 BYTE-SIZED FACT
In 1903, the U.S. Patent Office had a brief but real internal debate about closing entirely, on the theory that "everything that can be invented has been invented." They did not close. The next decade brought powered flight, the assembly line, and radio.
The Lesson: Every era has a moment where defenders feel like the ground has stopped moving. The attackers never get that memo. Plan as if your perimeter, your vendor list, and your threat model will all look different in 12 months. Because they will.
Found this valuable? Forward this to your team. The Cybervizer Newsletter
Questions, Suggestions & Sponsorships? Please email: [email protected]
Also, please subscribe (It is free) to my AI Bursts newsletter that provides “Actionable AI Insights in Under 3 Minutes from Global AI Thought Leader”.
You can follow me on X (Formerly Twitter) @mclynd for more cybersecurity and AI.

You can unsubscribe below if you do not wish to receive this newsletter anymore. Sorry to see you go, we will miss you!